Two U.K. teenagers have been convicted by a jury in London for being part of the notorious LAPSUS$ transnational gang and for orchestrating a series of brazen, high-profile hacks against major tech firms and demanding a ransom in exchange for not leaking the stolen information.
This includes Arion Kurtaj (aka White, Breachbase, WhiteDoxbin, and TeaPotUberHacker), an 18-year-old from Oxford, and an unnamed minor, who began collaborating in July 2021 after having met online, BBC reported this week.
Both the defendants were initially arrested and released under investigation in January 2022, only to be re-arrested and charged by the City of London Police in April 2022. Kurtaj was subsequently granted bail and moved to a hotel in Bicester after he was doxxed in an online cybercrime forum.
He, however, continued his hacking spree, targeting companies like Uber, Revolut, and Rockstar Games, as a result of which he was arrested again in September. Another alleged member of the group was apprehended by Brazilian authorities in October 2022.

Central to pulling off the extortion schemes was their ability to conduct SIM swapping and prompt bombing attacks to gain unauthorized access to corporate networks after an extensive social engineering phase.
The financially motivated operation also entailed posting messages to their Telegram channel to solicit rogue insiders who can provide Virtual Private Network (VPN), Virtual Desktop Infrastructure (VDI), or Citrix credentials to organizations.
A recent report from the U.S. government found that the actors offered as much as $20,000 per week for access to telecommunications providers so as to carry out the SIM swap attacks. It characterized LAPSUS$ as unique for its “effectiveness, speed, creativity, and boldness,” and for weaponizing a “playbook of effective techniques.”
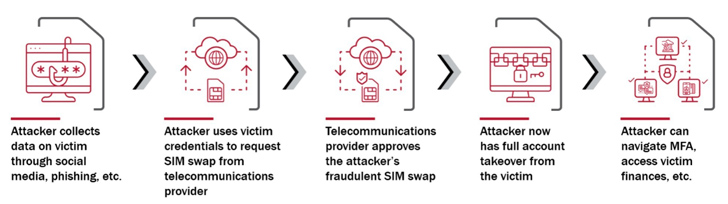
“To execute fraudulent SIM swaps, LAPSUS$ obtained basic information about its victims, such as their name, phone number, and customer proprietary network information (CPNI),” the Department of Homeland Security’s (DHS) Cyber Safety Review Board (CSRB) said.
“LAPSUS$ learned the information through a variety of ways, including issuing fraudulent [Emergency Disclosure Requests], and using account takeover techniques, to hijack the accounts of telecommunications provider employees and contractors.”

“It then performed fraudulent SIM swaps via the telecommunications provider’s customer management tools. After executing the fraudulent SIM swaps, LAPSUS$ took over online accounts via sign-in and account recovery workflows that sent one-time links or MFA passcodes via SMS or voice calls.”
Other methods of initial access ranged from employing the services of initial access brokers (IABs) to the exploitation of security flaws, following which the actors took steps to escalate privileges, laterally move across the network, set up persistent access via remote desktop software such as AnyDesk and TeamViewer, and disable security monitoring tools.
Among the firms infiltrated by LAPSUS$ comprised BT, EE, Globant, LG, Microsoft, NVIDIA, Okta, Samsung, Ubisoft, and Vodafone. It’s currently unclear whether ransoms were paid by any of the breached companies. The teenagers are expected to be sentenced at a later date.
“The group gained notoriety because it successfully attacked well-defended organizations using highly effective social engineering; targeted supply chains by compromising business process outsourcing (BPOs) and telecommunications providers; and used its public Telegram channel to discuss its operations, targets, and successes, and even to communicate with and extort its targets,” the CSRB said.
