A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information.
Cybersecurity company Securonix, which dubbed the campaign DEEP#GOSU, said it’s likely associated with the North Korean state-sponsored group tracked as Kimsuky.
“The malware payloads used in the DEEP#GOSU represent a sophisticated, multi-stage threat designed to operate stealthily on Windows systems especially from a network-monitoring standpoint,” security researchers Den Iuzvyk, Tim Peck, and Oleg Kolesnikov said in a technical analysis shared with The Hacker News.
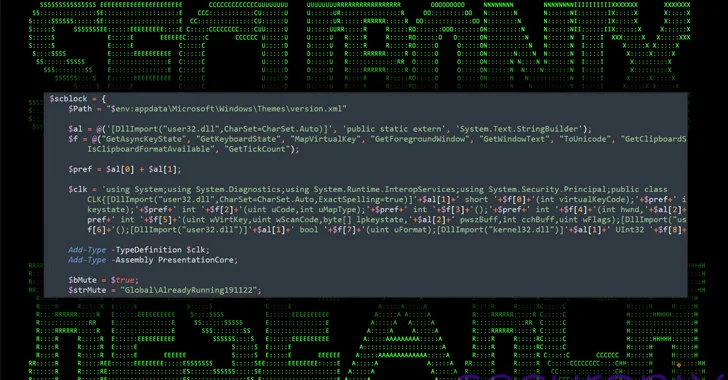
“Its capabilities included keylogging, clipboard monitoring, dynamic payload execution, and data exfiltration, and persistence using both RAT software for full remote access, scheduled tasks as well as self-executing PowerShell scripts using jobs.”
A notable aspect of the infection procedure is that it leverages legitimate services such as Dropbox or Google Docs for command-and-control (C2), thus allowing the threat actor to blend undetected into regular network traffic.
On top of that, the use of such cloud services to stage the payloads allows for updating the functionality of the malware or delivering additional modules.
The starting point is said to be a malicious email attachment containing a ZIP archive with a rogue shortcut file (.LNK) that masquerades as a PDF file (“IMG_20240214_0001.pdf.lnk”).
The .LNK file comes embedded with a PowerShell script as well as a decoy PDF document, with the former also reaching out to an actor-controlled Dropbox infrastructure to retrieve and execute another PowerShell script (“ps.bin”).

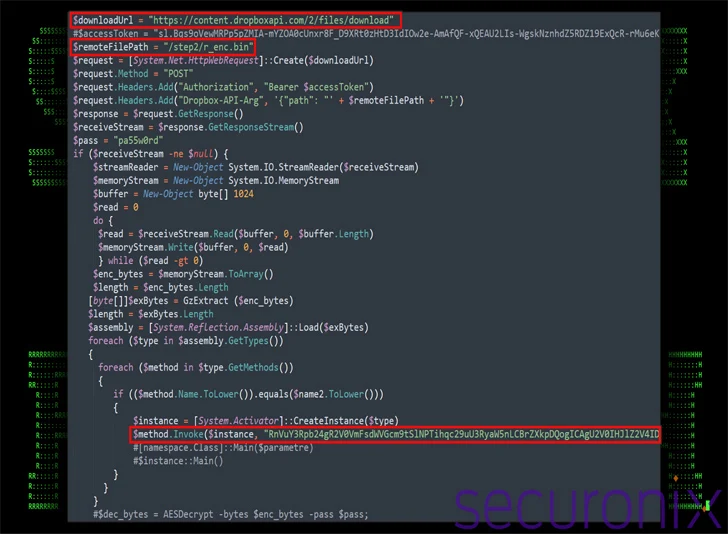
The second-stage PowerShell script, for its part, fetches a new file from Dropbox (“r_enc.bin”), a .NET assembly file in binary form that’s actually an open-source remote access trojan known as TruRat (aka TutRat or C# RAT) with capabilities to record keystrokes, manage files, and facilitate remote control.
It’s worth noting that Kimsuky has employed TruRat in at least two campaigns uncovered by the AhnLab Security Intelligence Center (ASEC) last year.
Also retrieved by the PowerShell script from Dropbox is a VBScript (“info_sc.txt”), which, in turn, is designed to run arbitrary VBScript code retrieved from the cloud storage service, including a PowerShell script (“w568232.ps12x”).
The VBScript is also designed to use Windows Management Instrumentation (WMI) to execute commands on the system, and set up scheduled tasks on the system for persistence.
Another noteworthy aspect of the VBScript is the use of Google Docs to dynamically retrieve configuration data for the Dropbox connection, allowing the threat actor to change the account information without having to alter the script itself.
The PowerShell script downloaded as a result is equipped to gather extensive information about the system and exfiltrate the details via a POST request to Dropbox.
“The purpose of this script appears to be designed to serve as a tool for periodic communication with a command-and-control (C2) server via Dropbox,” the researchers said. “Its main purposes include encrypting and exfiltrating or downloading data.”
In other words, it acts as a backdoor to control the compromised hosts and continuously keep a log of user activity, including keystrokes, clipboard content, and the foreground window.
The development comes as security researcher Ovi Liber detailed North Korea-linked ScarCruft’s embedding of malicious code within Hangul Word Processor (HWP) lure documents present in phishing emails to distribute malware like RokRAT.

“The email contains a HWP Doc which has an embedded OLE object in the form of a BAT script,” Liber said. “Once the user clicks on the OLE object, the BAT script executes which in turn creates a PowerShell-based reflective DLL injection attack on the victims machine.”
It also follows Andariel’s exploitation of a legitimate remote desktop solution called MeshAgent to install malware like AndarLoader and ModeLoader, a JavaScript malware meant for command execution.
“This is the first confirmed use of a MeshAgent by the Andariel group,” ASEC said. “The Andariel Group has been continuously abusing the asset management solutions of domestic companies to distribute malware in the process of lateral movement, starting with Innorix Agent in the past.”

Andariel, also known by the names Nicket Hyatt or Silent Chollima, is a sub-cluster of the notorious Lazarus Group, actively orchestrating attacks for both cyber espionage and financial gain.
The prolific state-sponsored threat actor has since been observed laundering a chunk of the crypto assets stolen from the hack of crypto exchange HTX and its cross-chain bridge (aka HECO Bridge) through Tornado Cash. The breach led to the theft of $112.5 million in cryptocurrency in November 2023.
“Following common crypto-laundering patterns, the stolen tokens were immediately swapped for ETH, using decentralized exchanges,” Elliptic said. “The stolen funds then lay dormant until March 13, 2024, when the stolen crypto assets began to be sent through Tornado Cash.”
The blockchain analytics firm said that Tornado Cash’s continuation of its operations despite sanctions have likely made it an attractive proposition for the Lazarus Group to conceal its transaction trail following the shutdown of Sinbad in November 2023.
“The mixer operates through smart contracts running on decentralized blockchains, so it cannot be seized and shut down in the same way that centralized mixers such as Sinbad.io have been,” it noted.