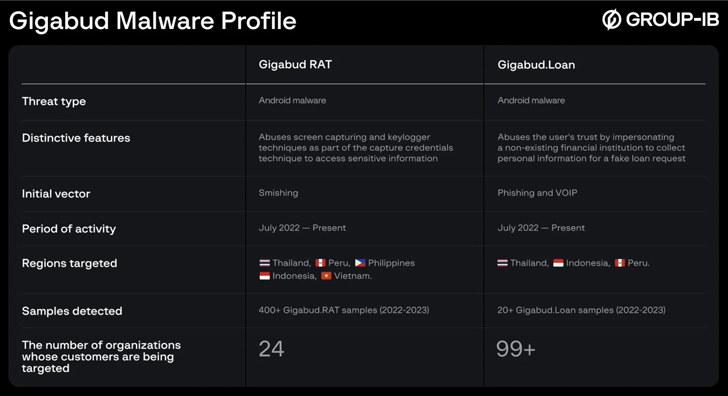
Account holders of over numerous financial institutions in Thailand, Indonesia, Vietnam, the Philippines, and Peru are being targeted by an Android banking malware called Gigabud RAT.
“One of Gigabud RAT’s unique features is that it doesn’t execute any malicious actions until the user is authorized into the malicious application by a fraudster, […] which makes it harder to detect,” Group-IB researchers Pavel Naumov and Artem Grischenko said.
“Instead of using HTML overlay attacks, Gigabud RAT gathers sensitive information primarily through screen recording.”
Gigabud RAT was first documented by Cyble in January 2023 after it was spotted impersonating bank and government apps to siphon sensitive data. It’s known to be active in the wild since at least July 2022.
The Singapore-based company said it also identified a second variant of the malware minus the RAT capabilities. Dubbed Gigabud.Loan, it comes under the guise of a loan application that’s capable of exfiltrating user-input data.
“The targets were individuals lured into filling out a bank card application form to obtain a low-interest loan,” the researchers said. “The victims are convinced to provide personal information during the application process.”
Both malware versions are spread via phishing websites, the links to which are delivered to victims via SMS or instant messages on social media networks. Gigabud.Loan is also distributed directly in the form of APK files sent through messages on WhatsApp.

Targets who are approached on social media are often coerced into visiting the sites under the pretext of completing a tax audit and claiming a refund.
While Android devices have the “Install from Unknown Sources” setting disabled by default as a security measure to prevent the installation of apps from untrusted sources, the operating system allows other apps on installed on the device, such as web browsers, email clients, file managers, and messaging apps, to request the “REQUEST_INSTALL_PACKAGES” permission.
Should a user grant permission to such apps, it allows the threat actors to install rogue APK files while bypassing the “Install from Unknown Sources” option.
Gigabud functions a lot like other Android banking trojans by requesting for accessibility services permissions to perform screen capturing and logging keystrokes. It’s also equipped to replace bank card numbers in clipboards and perform automated fund transfers through remote access.
On the other hand, Gigabud.Loan functions as a tool to collect personal information such as full name, identity number, national identity document photo, digital signature, education, income info, bank card information, and phone number under the guise of submitting a loan request to the bank.
The findings follow the discovery of 43 rogue apps on the Google Play Store that load ads while the device’s screen is turned off. The apps, with cumulative downloads of 2.5 million, have since been taken down or updated by the developers to remove the ad fraud component.
McAfee said the adware, once installed, seeks users’ permissions to exclude the apps when saving battery and allow it to draw over other apps, effectively opening the door to further malevolent attacks, such as loading ads in the background and displaying phishing pages.
The ad fraud library used by the apps also employs delay tactics to evade detection and can be remotely modified by the operators using the Firebase messaging service, lending it an additional layer of complexity.
The disclosure comes as the U.S. Federal Bureau of Investigation (FBI) is warning of an increase in scammers pretending to be recovery and tracing companies that can help victims of cryptocurrency investment scams regain lost assets.
“Recovery scheme fraudsters charge an up-front fee and either cease communication with the victim after receiving an initial deposit or produce an incomplete or inaccurate tracing report and request additional fees to recover funds,” the FBI said.

On top of that, the agency has cautioned that cybercriminals are embedding nefarious code in mobile beta-testing apps masquerading as legitimate cryptocurrency investment apps to defraud potential victims by facilitating the theft of personally identifiable information (PII) and financial account data.
“The apps may appear legitimate by using names, images, or descriptions similar to popular apps,” the agency explained. “Cyber criminals often use phishing or romance scams to establish communications with the victim, then direct the victim to download a mobile beta-testing app housed within a mobile beta-testing app environment, promising incentives such as large financial payouts.”
In these schemes, threat actors contact potential victims on dating and social networking apps and build trust with the ultimate aim to entice them into downloading pre-release versions of the apps.
“The victims enter legitimate account details into the app, sending money they believe will be invested in cryptocurrency, but instead the victim funds are sent to the cyber criminals,” the FBI said.
It’s worth noting that the abuse of Apple’s TestFlight beta testing framework to conduct pig butchering scams was highlighted by cybersecurity firm Sophos last year.
Recent waves of the campaign, also called CryptoRom, have weaponized Apple’s enterprise and developer ad-hoc app distribution schemes to deliver bogus crypto apps in a bid to slip past restrictions that prevent users from downloading iOS apps outside of the App Store.
In other instances, a seemingly innocuous app is trojanized after it is approved and published to the Apple and Google app storefronts by altering the remote code to point to an attacker-controlled server to introduce malicious behavior.
