An analysis of information-stealing malware logs published on the dark web has led to the discovery of thousands of consumers of child sexual abuse material (CSAM), indicating how such information could be used to combat serious crimes.
“Approximately 3,300 unique users were found with accounts on known CSAM sources,” Recorded Future said in a proof-of-concept (PoC) report published last week. “A notable 4.2% had credentials for multiple sources, suggesting a higher likelihood of criminal behavior.”
Over the past few years, off-the-shelf info-stealer variants have become a pervasive and ubiquitous threat targeting various operating systems with an aim to siphon sensitive information such as credentials, cryptocurrency wallets, payment card data, and screenshots.

This is evidenced in the rise of new stealer malware strains such as Kematian Stealer, Neptune Stealer, 0bj3ctivity, Poseidon (formerly RodStealer), Satanstealer, and StrelaStealer.
Distributed via phishing, spam campaigns, cracked software, fake update websites, SEO poisoning, and malvertising, data harvested using such programs typically find their way onto the dark web in the form of stealer logs from where they are purchased by other cybercriminals to further their schemes.

“Employees regularly save corporate credentials on personal devices or access personal resources on organizational devices, increasing the risk of infection,” Flare noted in a report last July.
“A complex ecosystem exists in which malware-as-a-service (MaaS) vendors sell info-stealer malware on illicit Telegram channels, threat actors distribute it through fake cracked software or phishing emails, and they then sell infected device logs on specialized dark web marketplaces.”
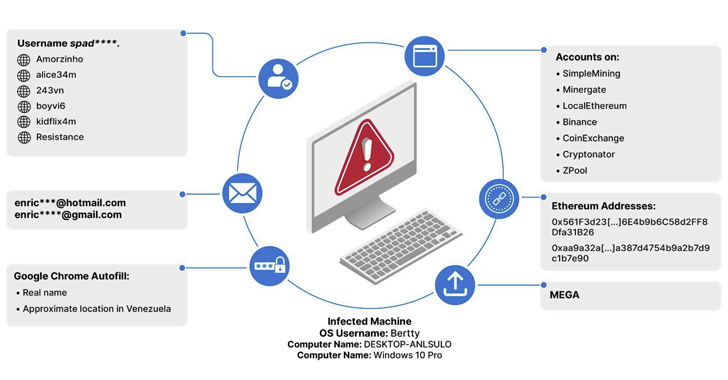
Recorded Future’s Insikt Group said it was able to identify 3,324 unique credentials used to access known CSAM domains between February 2021 and February 2024, using them to unmask three individuals who have been found to maintain accounts at no less than four websites.

The fact that stealer logs also comprise cryptocurrency wallet addresses means it could be used to determine if the addresses have been used to procure CSAM and other harmful material.
Furthermore, countries like Brazil, India, and the U.S. had the highest counts of users with credentials to known CSAM communities, although the company said that it could be due to an “overrepresentation due to dataset sourcing.”
“Info-stealer malware and stolen credentials are projected to remain a cornerstone of the cybercriminal economy due to the high demand by threat actors seeking initial access to targets,” it said, adding it has shared its findings with law enforcement.
“Info-stealer logs can be used by investigators and law enforcement partners to track child exploitation on the dark web and provide insight into a part of the dark web that is especially difficult to trace.”