The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne show.
The cybersecurity firm also confirmed connections between the malware and AcidRain, tying it to threat activity clusters associated with Russian military intelligence.
“AcidPour’s expanded capabilities would enable it to better disable embedded devices including networking, IoT, large storage (RAIDs), and possibly ICS devices running Linux x86 distributions,” security researchers Juan Andres Guerrero-Saade and Tom Hegel said.
AcidPour is a variant of AcidRain, a wiper that was used to render Viasat KA-SAT modems operable at the onset of the Russo-Ukrainian war in early 2022 and cripple Ukraine’s military communications.

It also builds upon the latter’s features, while targeting Linux systems running on x86 architecture. AcidRain, on the other hand, is compiled for MIPS architecture.
Where AcidRain was more generic, AcidPour incorporates logic to target embedded devices, Storage Area Networks (SANs), Network Attached Storage (NAS) appliances, and dedicated RAID arrays.
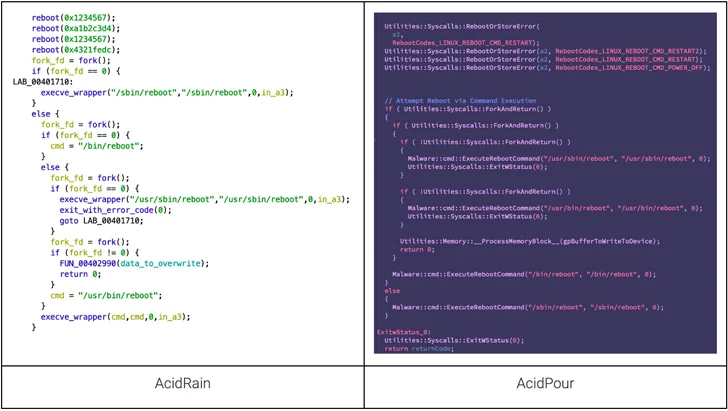
That said, both the strains overlap when it comes to the use of the reboot calls and the method employed for recursive directory wiping. Also identical is the IOCTLs-based device-wiping mechanism that also shares commonalities with another malware linked to Sandworm known as VPNFilter.
“One of the most interesting aspects of AcidPour is its coding style, reminiscent of the pragmatic CaddyWiper broadly utilized against Ukrainian targets alongside notable malware like Industroyer 2,” the researchers said.
The C-based malware comes with a self-delete function that overwrites itself on disk at the beginning of its execution, while also employing an alternate wiping approach depending on the device type.
AcidPour has been attributed to a hacking crew tracked as UAC-0165, which is associated with Sandworm and has a track record of striking Ukrainian critical infrastructure.
The Computer Emergency Response Team of Ukraine (CERT-UA), in October 2023, implicated the adversary to attacks targeting at least 11 telecommunication service providers in the country between May and September of last year.

“[AcidPour] could have been used in 2023,” Hegel told The Hacker News. “It’s likely the actor has made use of AcidRain/AcidPour related tooling consistently throughout the war. A gap in this perspective speaks to the level of insight the public often has to cyber intrusions – generally quite limited and incomplete.”
The ties to Sandworm are further bolstered by the fact that a threat actor known as Solntsepyok (aka Solntsepek or SolntsepekZ) claimed to have infiltrated four different telecommunication operators in Ukraine and disrupted their services on March 13, 2024, three days prior to the discovery of AcidPour.
Solntsepyok, according to the State Special Communications Service of Ukraine (SSSCIP), is a Russian advanced persistent threat (APT) with likely ties to the Main Directorate of the General Staff of the Armed Forces of the Russian Federation (GRU), which also operates Sandworm.
It’s worth pointing out that Solntsepyok has also been accused of hacking into Kyivstar’s systems as early as May 2023. The breach came to light in late December.
While it’s currently not clear if AcidPour was used in the latest set of attacks, the discovery suggests that threat actors are constantly refining their tactics to stage destructive assaults and inflict significant operational impact.
“This progression reveals not only a refinement in the technical capabilities of these threat actors but also their calculated approach to select targets that maximize follow-on effects, disrupting critical infrastructure and communications,” the researchers said.
