A sophisticated phishing campaign is using a Microsoft Word document lure to distribute a trifecta of threats, namely Agent Tesla, OriginBotnet, and OriginBotnet, to gather a wide range of information from compromised Windows machines.
“A phishing email delivers the Word document as an attachment, presenting a deliberately blurred image and a counterfeit reCAPTCHA to lure the recipient into clicking on it,” Fortinet FortiGuard Labs researcher Cara Lin said.
Clicking on the image leads to the delivery of a loader from a remote server that, in turn, is designed to distribute OriginBotnet for keylogging and password recovery, RedLine Clipper for cryptocurrency theft, and Agent Tesla for harvesting sensitive information.
The loader, written in .NET, employs a technique called binary padding by adding null bytes to increase the file’s size to 400 MB in an attempt to evade detection by security software.

The activation of the loader triggers a multi-stage process to establish persistence on the host and extract a dynamic-link library (DLL) that’s responsible for unleashing the final payloads.
One among them is RedLine Clipper, a .NET executable for stealing cryptocurrencies by tampering with the user’s system clipboard to substitute the destination wallet address with an attacker-controlled one.
“To carry out this operation, RedLine Clipper utilizes the ‘OnClipboardChangeEventHandler’ to regularly monitor clipboard changes and verify if the copied string conforms to the regular expression,” Lin said.
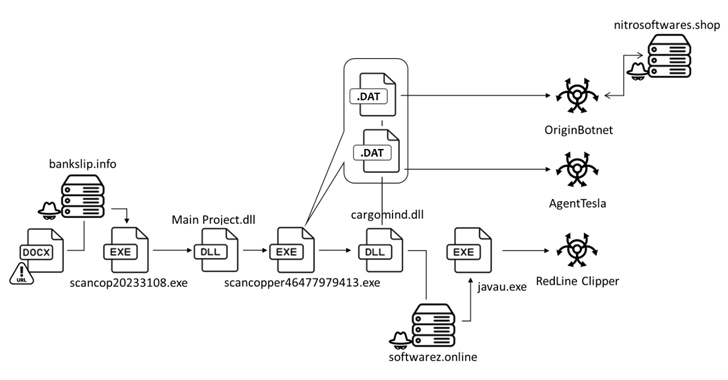
Agent Tesla, on the other hand, is a .NET-based remote access trojan (RAT) and data stealer for gaining initial access and exfiltrating sensitive information such as keystrokes and login credentials used in web browsers to a command-and-control (C2) server over SMTP protocol.
Also delivered is a new malware dubbed OriginBotnet, which packs in a wide range of features to collect data, establish communications with its C2 server, and download supplementary plugins from the server to execute keylogging or password recovery functions on compromised endpoints.
Way Too Vulnerable: Uncovering the State of the Identity Attack Surface
Achieved MFA? PAM? Service account protection? Find out how well-equipped your organization truly is against identity threats
Supercharge Your Skills
“The PasswordRecovery plugin retrieves and organizes the credentials of various browser and software accounts,” Lin said. “It records these results and reports them via HTTP POST requests.”
It’s worth noting that Palo Alto Networks Unit 42, in September 2022, detailed an Agent Tesla successor called OriginLogger, which comes with similar features as that of OriginBotnet, suggesting that they could be both the work of the same threat actor.
“This cyberattack campaign […] involved a complex chain of events,” Fortinet said. “It began with a malicious Word document distributed via phishing emails, leading victims to download a loader that executed a series of malware payloads. The attack demonstrated sophisticated techniques to evade detection and maintain persistence on compromised systems.”
